Definitions[]
Cryptography (from the Greek meaning "secret writing") is
| “ | the discipline that embodies principles, means, and methods for providing information security, including confidentiality, data integrity, nonrepudiation, and authenticity.[1] | ” |
| “ | a branch of mathematics that deals with the transformation of data. Transformation converts ordinary text (plaintext) into coded form (ciphertext) by encryption; and ciphertext into plaintext by decryption.[2] | ” |
| “ | a fundamental mechanism used to protect the confidentiality and integrity of critical and sensitive information.[3] | ” |
Overview[]
Cryptography is used to secure transactions by providing ways to ensure data confidentiality (assurance that the information will be protected from unauthorized access), data integrity (assurance that data have not been accidentally or deliberately altered), authentication of the message’s originator, electronic certification of data, and non-repudiation (proof of the integrity and origin of data that can be verified by a third party). Accordingly, cryptography has an important role in protecting information both within a computer system and when information is sent over the Internet and other unprotected communications channels. A basic element of cryptography is encryption.
| “ | Cryptography involves the use of mathematical functions called algorithms and strings of seemingly random bits called keys to (1) encrypt a message or file so that it is unintelligible to those who do not have the secret key needed to encrypt it, thus keeping the contents of the message or file confidential; (2) provide an electronic signature that can be used to determine if any changes have been made to the related file, thus ensuring the file's integrity; or (3) link a message or document to a specific individual's or group's key, thus ensuring that the "signer" of the file can be identified.[4] | ” |
Encryption is the process of transforming ordinary data (commonly referred to as plaintext) into code form (ciphertext) using a special value known as a key and a mathematical process called an algorithm. Cryptographic algorithms are designed to produce ciphertext that is unintelligible to unauthorized users. Decryption of ciphertext is possible only by using the proper key.
Encryption technologies can be used on data to (1) hide their information content, (2) prevent their undetected modification, and (3) prevent their unauthorized use. When properly implemented, encryption technologies can provide assurance regarding the confidentiality, integrity, or origin of information that has been exchanged. It can also provide a method by which the authenticity of a document can be confirmed.
A basic premise in cryptography is that good systems depend only on the secrecy of the key used to perform the operations and not on the secrecy of the algorithm. The algorithms used to perform most cryptographic operations over the Internet are well known. However, because the keys used by these algorithms are kept secret, the process is considered secure.
Cryptographic techniques[]
Cryptographic techniques can be divided into two basic types: secret key cryptography and public key cryptography. Each type has its strengths and weaknesses, and systems that utilize both forms are used to take advantage of the strengths of a given type.
Several levels of cryptographic technology are currently in use. Cryptographic modules implement algorithms that form the building blocks of cryptographic applications. Using these modules, technologies are available that can be used to encrypt message transmissions so that eavesdroppers cannot determine the contents of the message. Digital signature technologies use cryptography to authenticate the sender of a message. Hash technologies use cryptography to provide assurance to a message recipient that the contents of the message have not been altered.
Several cryptographic technologies are used to ensure the confidentiality and integrity of data as it is being transmitted over the network. These technologies include digital certificates, digital signatures, secure sockets layer (SSL), and virtual private networks (VPN). Many of these technologies are built into applications that are commonly available on many computer systems. For example, most Web browsers support SSL for secure communications between a computer and the Web server.
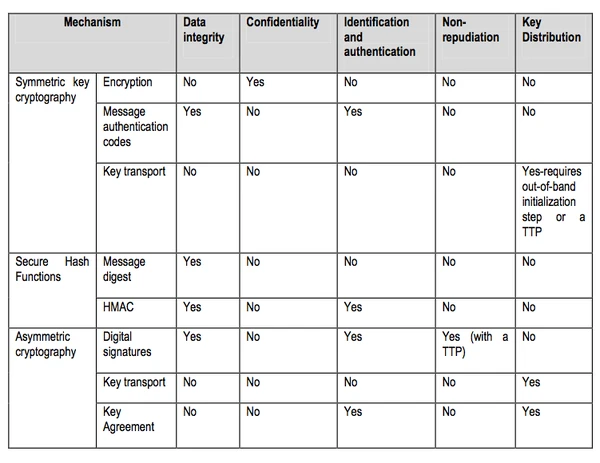
The following table provides a summary of the characteristics of cryptographic techniques:
Cryptographic policy[]
Cryptography has become a technology of broad application; thus, decisions about cryptography policy have increasingly broad effects on society. The effects of policies about cryptography are not limited to technological developments in cryptography, or even to the health and vitality of companies that produce or use products incorporating cryptography. Instead, these policies will increasingly affect the everyday lives of most citizens: cryptography will be used to help ensure the confidentiality and integrity of health records and tax returns; it will help speed the way to electronic commerce; and it will help manage copyrighted material in electronic form.
Policy debate over cryptography used to be as arcane as the technology itself. Most people did not regard government decisions about cryptography as directly affecting their lives. However, as the communications technologies used in daily life have changed, concern over the implications of privacy and security policies dominated by national security objectives has grown dramatically, particularly in business and academic communities that produce or use information safeguards, but among the general public as well.
Previously, control of the availability and use of cryptography was presented as a national security issue focused outward, with the intention of maintaining a U.S. technological lead over other countries. Now, with an increasing policy focus on domestic crime and terrorism, the availability and use of cryptography has also come into prominence as a domestic-security, law-enforcement issue. More widespread foreign use of cryptography — including use by terrorists and developing countries — makes U.S. signals intelligence more difficult. Within the United States, cryptography is increasingly portrayed as a threat to domestic security (public safety) and a barrier to law enforcement if it is readily available for use by terrorists or criminals. There is also growing recognition of the potential misuses of cryptography, such as by disgruntled employees as a means to sabotage an employer’s databases. Thus, export controls, intended to restrict the international availability of U.S. cryptography technology and products, are now being joined with domestic cryptography initiatives intended to preserve U.S. law-enforcement and signals-intelligence capabilities.
References[]
- ↑ NIST Special Publication 800-21 (2d ed.).
- ↑ DHS Sensitive Systems Policy Directive 4300A, at 87.
- ↑ Information Security: National Archives and Records Administration Needs to Implement Key Program Elements and Controls, at 11.
- ↑ Information Security: IRS Needs to Address Control Weaknesses That Place Financial and Taxpayer Data at Risk, at 8-9.
See also[]
- Ancillary cryptography
- Asymmetric cryptography
- Computer cryptography
- Cryptanalysis
- Cryptanalytic
- Crypto group
- Cryptochannel
- Crypto-equipment
- Cryptographer
- Cryptographic algorithm
- Cryptographic boundary
- Cryptographic chaining
- Cryptographic checkvalue
- Cryptographic defense
- Cryptographic hash function
- Cryptographic information
- Cryptographic key
- Cryptographic key lifecycle
- Cryptographic key management system
- Cryptographic key pair
- Cryptographic Message Syntax
- Cryptographic module
- Cryptographic module security policy
- Cryptographic protocol
- Cryptography Standards and Infrastructures for the Twenty-First Century
- Cryptographic strength
- Cryptography control
- Cryptologic
- Cryptology
- Cryptography’s Role in Securing the Information Society
- Cryptologic activities
- Cryptology
- Cryptomaterial
- DNA cryptography
- Embedded cryptography
- Guidelines for Cryptography Policy
- Guideline for Implementing Cryptography In the Federal Government
- Minimalist cryptography
- National Cryptography Policy
- Open cryptographic interface
- Post-quantum cryptography
- Private key cryptography
- Public Cryptography Study Group
- Public key cryptography
- Public Key Cryptography Standard
- Quantum cryptography
- Report on Background and Issues of Cryptography Policy
- Secret key cryptography
- Symmetric cryptography
- Symmetric key cryptography
- Symmetric key cryptosystem
- Type I cryptography
- Type II cryptography
- Type III cryptography
- Type III(E) cryptography